“Brute force attack” sounds like someone crashing into your website, and reality is not very different from that image. A brute force attack occurs when a computer manages to identify the user name of the administrator, owner or users of other types of profile. The next thing he does is to automatically try to access the web by guessing the password and for this they use dictionaries of more than 10 GB that contain passwords, which in turn are randomly combined again and again.
If the attack is successful, it can make you lose your web, settings, content and sensitive information. If the attack fails to access your website, it’s still damaged because so many attempts to input exhaust server resources, which causes it to show a memory problem message to users.
How can we prevent these attacks from wreaking havoc on a web page? There are many tips!
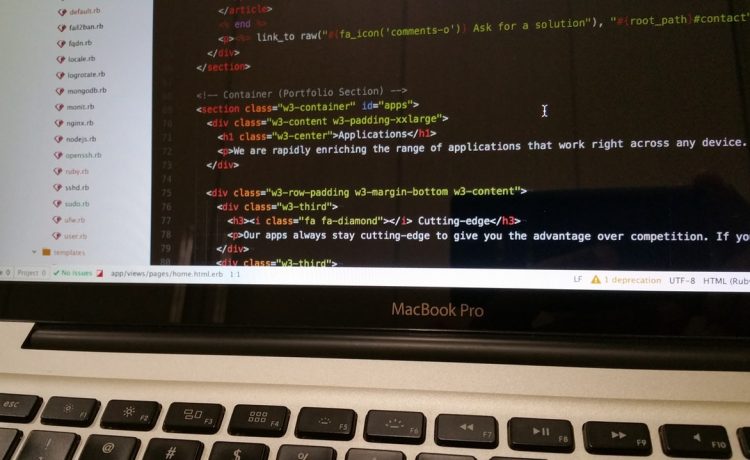
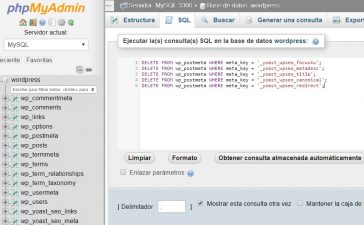
Change the wp_ prefix of the database
It’s almost always the host who is going to provide you with the information to be able to communicate WordPress with your database, but it is also very common that the prefix of these files or tables is always “wp_”. As it’s so common, hackers know it and can extract information from there. When you install your WordPress it starts by changing that prefix, it doesn’t have to be a long or complicated name, only a particular one that you can recognize.
Change the username
Never forgetting this: Don’t use the name “admin” as a username, even if it’s easy, fast, it does not matter. You can change the username with a plugin like Username Changer (there’s more, but this is the most popular) or do it from the WordPress database.
Keep your WordPress updated
WordPress updates, plugins, themes, etc. they always bring improvements in terms of security. Keep your WordPress updated (which you can automate), including major updates.
Don’t use easy passwords
Just as it’s not advisable to use your birthday as a password at an ATM, don’t use too predictable passwords like yourname123 or similar. If you have the option, install plugins like Force Strong Passwords that will notify users when the password is weak. You can also use password banks like LastPass, 1Password or Google Lock.
If you don’t use the previous three, anyway use passwords that include uppercase, lowercase, numbers, special characters and that are more than 8 characters; for example, #PerroPeludo*25.
Keep the plugins up to date
Plugins can be a gateway in case of attacks, so it is better to install plugins from reliable sources and to be constantly updated.
Keep the theme updated
Whether downloaded from WordPress or from an independent website, it fixes a periodic review of the updates of the topics, since as the topics are not updated as often as a plugin or application can be updated, hackers have more time to learn about them and cause more damage.
Don’t access your website from / wp-admin
You can change the URL of / wp-admin to a different URL to confuse hackers, this is achieved with plugins like Loginizer or some extremely simple as WPS Hide Login.
Use different addresses to what could be predictable, change / access by / equipment or something similar.
It is also possible to do it manually, consulting specialized blogs such as Elegant Themes, WordPress or Stack Overflow.
Back your website
Check that your hosting makes full, automatic and periodic backups. BackWPup is a very popular plugin and recommended to generate these backups on another server, send them by mail and automate the generation of them.